Our services
Pricing Plans
Startup
 Transparent traffic delivery
Transparent traffic delivery Basic traffic filtering
Basic traffic filtering End-to-end TLS encryption
End-to-end TLS encryption
Your traffic remains encrypted throughout the entire path to the web application
 No IP address changes
No IP address changes Integration without DNS changes
Integration without DNS changes Support response time up to 2 hours
Support response time up to 2 hoursBusiness
Popular
 Reverse proxy
Reverse proxy Anti-scanning protection
Anti-scanning protection Support via messaging apps
Support via messaging apps Free SSL certificate
Free SSL certificate WebSocket support
WebSocket support Custom filtering rules
Custom filtering rules Adaptive GEO-blocking
Adaptive GEO-blocking Dedicated IP-address
Dedicated IP-address Support response time up to 30 minutes
Support response time up to 30 minutesHow DDoS attack protection works?
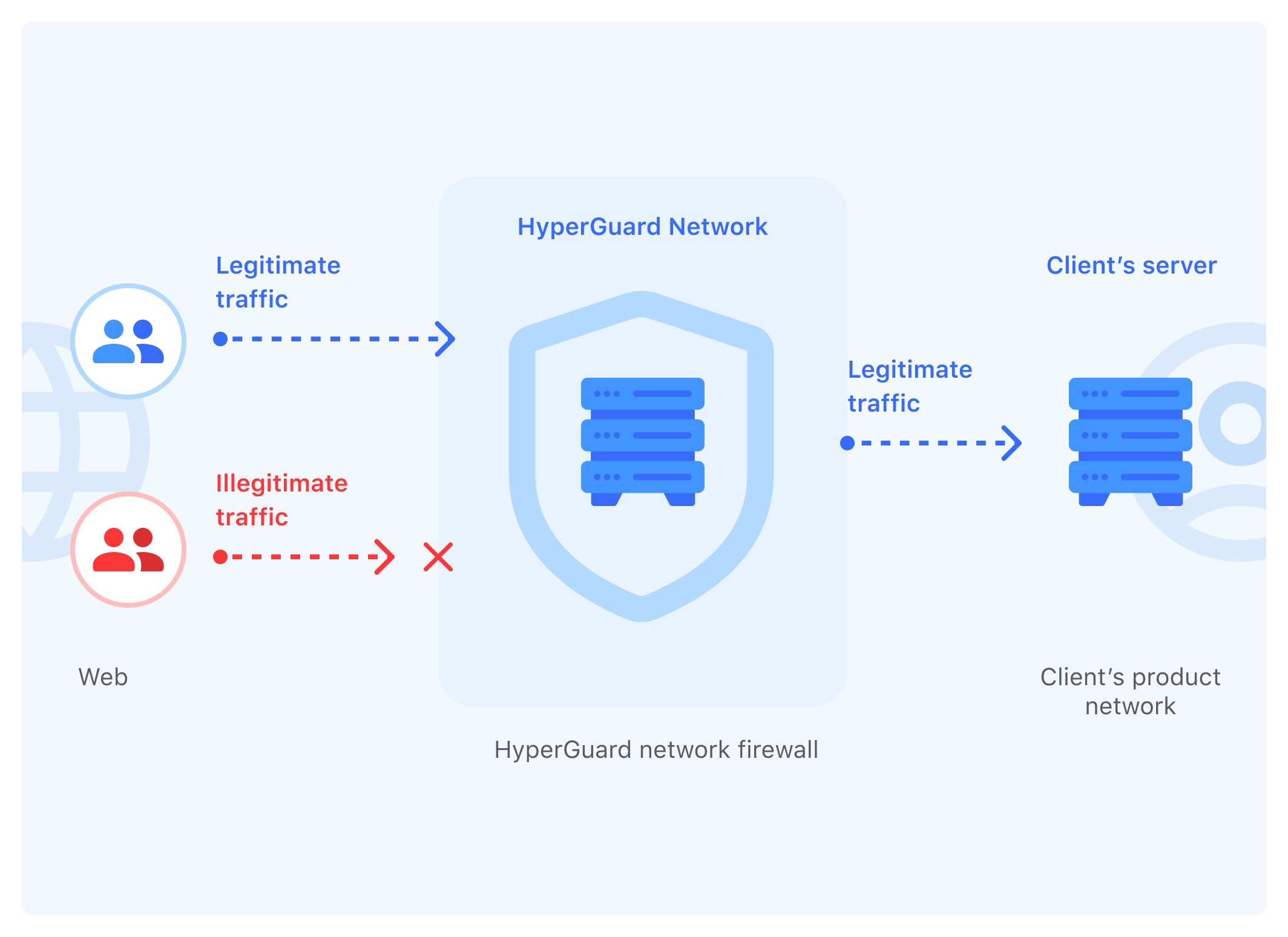
We connect your website to our filtering network. The connection method depends on where your server is hosted
From now on, all DDoS attacks targeting your site will be redirected to our network hardware.
We will filter all traffic and allow legitimate users only.
Notice! We can activate protection remotely or within our network.

Advantages of our service
Transparent traffic control
Capable to withstand terabit attacks
Works in the background mode and doesn't require CAPTCHA input
Fully integrated with any systems
High loading speed by Geo-Distributed system
Scales according to the growth rate of the project
Which services needs protection?
The number of cyber-attacks is increasing every year. More and more companies are becoming an easy target for both competitors and criminals.The financial sector
Banks, exchanges and payment systems are losing the trust of customers
E-commerce
Online stores are losing customers
Online games
The entertainment industry is losing players and audiences
Cellular carriers
Losing customers and seven-figure amounts
Educational platforms
Educational institutions are losing access to accounting and teaching tools
Courier services
Services are losing profit and incurring significant costs due to courier downtime
The public sector
Government portals are inaccessible during important events
Data centers
DDoS attacks account for the main percentage of costs




